What Is Check Tampering
adminse
Apr 01, 2025 · 8 min read
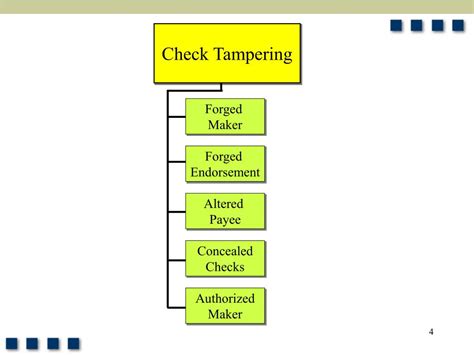
Table of Contents
Unmasking Check Tampering: A Comprehensive Guide to Fraudulent Alterations
What if the seemingly simple act of writing a check harbors the potential for significant financial loss? Check tampering, a pervasive form of fraud, represents a serious threat to individuals and businesses alike.
Editor’s Note: This comprehensive article on check tampering was published today, providing readers with up-to-date insights and actionable strategies to prevent and detect this insidious form of financial crime.
Why Check Tampering Matters: Relevance, Practical Applications, and Industry Significance
Check tampering remains a significant concern despite the rise of digital payments. The ease with which checks can be altered, coupled with the relatively low level of security measures often employed, makes them a tempting target for fraudsters. The implications extend beyond simple monetary loss; damaged reputations, legal battles, and eroded trust can result from even a single instance of check tampering. Understanding check tampering is crucial for individuals, businesses, and financial institutions to protect themselves from significant financial and reputational harm. This includes understanding the various methods used, identifying red flags, and implementing effective prevention strategies.
Overview: What This Article Covers
This article provides a deep dive into the world of check tampering. We will explore various methods used to alter checks, discuss the legal ramifications, delve into prevention strategies for individuals and businesses, and examine the role of technology in mitigating this type of fraud. Readers will gain a comprehensive understanding of how to identify fraudulent checks and protect themselves from becoming victims.
The Research and Effort Behind the Insights
This article draws upon extensive research, incorporating insights from law enforcement agencies, financial institutions, and fraud prevention experts. Data from reported cases, legal precedents, and best practices in fraud detection are utilized to ensure accuracy and provide readers with reliable information. The structured approach ensures a clear and comprehensive understanding of this complex issue.
Key Takeaways:
- Definition and Core Concepts: A clear definition of check tampering and its various forms.
- Methods of Tampering: Detailed explanations of common techniques used to alter checks.
- Legal Ramifications: A discussion of the legal penalties associated with check tampering.
- Prevention Strategies: Actionable steps individuals and businesses can take to prevent check tampering.
- Detection Techniques: Methods for identifying altered or fraudulent checks.
- The Role of Technology: How technology is being used to combat check tampering.
Smooth Transition to the Core Discussion:
With a firm understanding of the significance of check tampering, let's explore the intricacies of this crime, examining the techniques employed, the legal consequences, and the effective measures to safeguard against it.
Exploring the Key Aspects of Check Tampering
1. Definition and Core Concepts:
Check tampering involves the unauthorized alteration of a check to increase the amount payable, change the payee, or otherwise modify the check's details for fraudulent gain. This differs from check forgery, which involves creating a completely fake check. Tampering focuses on modifying a legitimate check. It encompasses a range of actions, including:
- Amount alteration: Increasing the numerical amount payable on the check.
- Payee alteration: Changing the name of the recipient to redirect funds to a fraudulent account.
- Date alteration: Modifying the date to extend the check's validity or circumvent stop-payment orders.
- Check washing: Removing ink from the check using chemicals to rewrite the details.
2. Methods of Tampering:
The methods employed by check tampered are often sophisticated, relying on subtle changes that may be difficult to detect without careful examination. Common techniques include:
- Using correction fluid: Applying correction fluid or similar products to obliterate existing information and rewrite new details. This is often detectable under UV light.
- Chemical alteration: Employing chemical solvents to remove ink, allowing the fraudster to rewrite the check's information.
- Using sophisticated printing techniques: Employing advanced printing methods to create convincing alterations that blend seamlessly with the original check information. This often involves forging signatures.
- Photo manipulation: Digitally altering a check image and then printing a modified version.
3. Legal Ramifications:
Check tampering is a serious crime with severe legal consequences. Penalties vary depending on the jurisdiction and the amount of money involved. Consequences can include:
- Felony charges: In most cases, check tampering constitutes a felony offense, resulting in lengthy prison sentences.
- Significant fines: Individuals found guilty of check tampering can face substantial financial penalties.
- Restitution: Victims are often entitled to restitution to recover their losses.
- Civil lawsuits: Victims may also pursue civil lawsuits against the perpetrators to recover damages.
4. Prevention Strategies for Individuals and Businesses:
Preventing check tampering requires a multi-faceted approach encompassing both physical and procedural safeguards. Key preventative measures include:
- Using high-security checks: Opting for checks with advanced security features, such as specialized paper, microprinting, or embedded security threads.
- Using check-writing software: Employing check-writing software to minimize the risk of manual alterations.
- Using void checks appropriately: Properly voiding checks that are no longer needed and securely disposing of them.
- Regularly reconciling bank statements: Diligent review of bank statements to promptly identify any discrepancies or unauthorized transactions.
- Implementing strong internal controls: For businesses, this includes segregating duties, requiring dual authorization for check issuance, and maintaining meticulous records.
- Employee training: Educating employees about check tampering, its methods, and the importance of vigilance.
5. Detection Techniques:
Detecting check tampering requires careful scrutiny of the check itself. Key aspects to examine include:
- Examine the ink: Check for variations in ink color, inconsistencies in writing style, or signs of erasure.
- Look for alterations: Scrutinize the numerical amount, payee name, and date for any alterations or inconsistencies.
- Use UV light: Use ultraviolet light to detect traces of correction fluid or other chemical alterations.
- Check for signs of tampering: Look for signs of alteration, such as smudges, faint lines, or uneven ink.
6. The Role of Technology:
Technology plays an increasingly crucial role in combating check tampering. This includes:
- High-resolution scanners: Employing scanners with high-resolution capabilities to capture subtle variations in ink or paper.
- Fraud detection software: Utilizing software that analyzes check images for inconsistencies and identifies potential signs of tampering.
- Check verification systems: Implementing systems that verify check authenticity and detect potential fraudulent activity.
Exploring the Connection Between Encryption and Check Tampering
While not directly involved in the alteration process, strong encryption plays a vital role in protecting electronic check transmission. Encryption ensures that the data transmitted between parties remains confidential and unaltered during transmission, mitigating the risk of someone intercepting and modifying the check information before it reaches the bank.
Key Factors to Consider:
- Roles and Real-World Examples: Encryption's role is paramount in online banking and electronic check processing. A real-world example involves online bill pay systems where checks are processed electronically; robust encryption safeguards the transaction's integrity.
- Risks and Mitigations: Weak encryption or lack thereof exposes electronic checks to significant risk of alteration. Mitigations involve using strong encryption algorithms and ensuring secure transmission protocols.
- Impact and Implications: Successful encryption prevents tampering during transmission but doesn't eliminate the risk of tampering after the check is printed and handled physically.
Conclusion: Reinforcing the Connection
The interplay between robust encryption in electronic check systems and the physical security measures needed to prevent check tampering emphasizes the layered approach necessary for comprehensive protection against this type of fraud. Encryption plays a crucial role in securing electronic transmission, while vigilant security measures are essential for the physical handling of checks.
Further Analysis: Examining Encryption in Greater Detail
Encryption technology, involving algorithms that transform readable data into an unreadable format, serves as a cornerstone of modern data security. This extends to financial transactions, where encryption protocols such as TLS/SSL and others protect sensitive financial information, reducing the vulnerability of electronic checks to manipulation during transmission.
FAQ Section: Answering Common Questions About Check Tampering
Q: What is the most common method of check tampering?
A: Amount alteration, where the numerical value of the check is increased, remains a prevalent method due to its relative simplicity.
Q: Can I prosecute someone for check tampering myself?
A: No. Check tampering is a criminal offense, and prosecution must be handled by law enforcement agencies. You should report the crime to your local police department and your bank.
Q: What should I do if I suspect check tampering?
A: Immediately contact your bank to report the suspected fraud and stop payment on the check. Gather all relevant documentation and cooperate fully with law enforcement investigations.
Practical Tips: Maximizing the Benefits of Check Tampering Prevention
- Use pre-printed checks with security features.
- Store unused checks securely.
- Reconcile your bank statements regularly.
- Report suspicious activity immediately.
- Educate employees about check tampering prevention (for businesses).
Final Conclusion: Wrapping Up with Lasting Insights
Check tampering remains a significant threat, demanding a proactive and multi-faceted approach to prevention and detection. By understanding the methods employed, implementing robust security measures, and utilizing technological advancements, individuals and businesses can significantly reduce their vulnerability to this form of financial crime. Vigilance, coupled with a comprehensive understanding of the risks and available safeguards, is paramount in safeguarding against the financial and reputational ramifications of check tampering.
Latest Posts
Latest Posts
-
How Does Liquidity Mining Work
Apr 03, 2025
-
What Is Binance Liquidity Mining
Apr 03, 2025
-
What Is Eth Liquidity Mining
Apr 03, 2025
-
What Is Liquidity Mining In Blockchain
Apr 03, 2025
-
What Is Liquidity Mining In Cryptocurrency
Apr 03, 2025
Related Post
Thank you for visiting our website which covers about What Is Check Tampering . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.