Check Fraudsters
adminse
Apr 01, 2025 · 7 min read
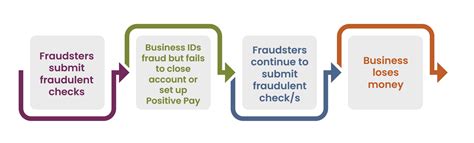
Table of Contents
Unmasking the Masters of Deception: A Deep Dive into Check Fraud
What if the seemingly simple act of writing a check harbors a complex web of sophisticated fraud schemes? Check fraud, perpetrated by cunning individuals known as check fraudsters, is a pervasive threat impacting businesses and individuals alike.
Editor’s Note: This article on check fraudsters provides an in-depth analysis of their methods, motivations, and the fight against this evolving crime. The information presented is current and based on the latest research and law enforcement reports.
Why Check Fraud Matters: A Looming Threat in the Digital Age
While digital transactions dominate modern commerce, the humble check remains a surprisingly prevalent method of payment, particularly in smaller businesses and personal transactions. This persistence makes it a tempting target for check fraudsters, who exploit vulnerabilities in the system for financial gain. The consequences of check fraud extend beyond the immediate financial losses; it erodes trust in traditional payment methods and increases the costs for businesses and financial institutions. The sheer volume of fraudulent checks processed annually represents a significant drain on the economy, demanding proactive prevention and robust investigation techniques.
Overview: What This Article Covers
This article delves into the multifaceted world of check fraudsters, exploring their diverse methods, the psychological profiles often associated with them, the challenges faced by law enforcement and financial institutions in combating this crime, and the preventative measures individuals and businesses can take. Readers will gain a comprehensive understanding of this evolving threat and actionable strategies for protection.
The Research and Effort Behind the Insights
This article synthesizes information from multiple sources, including reports from the FBI, the Federal Trade Commission (FTC), academic research on financial crime, and interviews with law enforcement professionals specializing in fraud investigation. The data analyzed reflects current trends and emerging tactics employed by check fraudsters.
Key Takeaways:
- Types of Check Fraud: A detailed examination of various check fraud schemes, from forgery and alteration to counterfeit checks and account takeover.
- Profiles of Check Fraudsters: An exploration of the diverse backgrounds and motivations driving individuals to engage in check fraud.
- Law Enforcement Challenges: The obstacles faced by investigators in tracking and prosecuting check fraudsters.
- Preventive Measures: Practical strategies for individuals and businesses to mitigate their risk of becoming victims.
- Technological Advancements in Fraud Detection: An overview of the evolving technologies used to combat check fraud.
Smooth Transition to the Core Discussion:
Understanding the motivations and methods of check fraudsters is crucial for effective prevention and prosecution. Let's examine the key aspects of this sophisticated criminal activity.
Exploring the Key Aspects of Check Fraud
1. Types of Check Fraud:
Check fraudsters employ a range of techniques, each demanding different investigative approaches. These include:
-
Forged Checks: Fraudsters create counterfeit checks using stolen or fabricated information, often mimicking legitimate check designs. This involves sophisticated counterfeiting techniques and access to printing equipment.
-
Altered Checks: Legitimate checks are altered by changing the payee, amount, or date. This requires careful manipulation to avoid detection, often involving chemical treatments or sophisticated printing technology.
-
Counterfeit Checks: Fraudsters produce entirely fake checks, utilizing high-quality printing and mimicking the security features of genuine checks from various banks. This sophisticated method requires significant technical expertise.
-
Account Takeover: Fraudsters gain unauthorized access to a victim's bank account and write fraudulent checks from the compromised account. This can involve phishing scams, malware, or insider collusion.
-
Check Kiting: This involves writing checks from one account to another, taking advantage of float time to create a false balance. This is a more sophisticated scheme often involving multiple accounts.
2. Profiles of Check Fraudsters:
The stereotype of a check fraudster as a lone wolf operating from a dimly lit basement is often inaccurate. Check fraud involves a spectrum of individuals, including:
-
Organized Crime Rings: Sophisticated operations with complex networks, often involving international connections and advanced technology.
-
Opportunistic Individuals: Individuals who seize opportunities to commit check fraud, often driven by financial desperation or addiction.
-
Insider Threats: Employees with access to sensitive information within businesses or financial institutions who exploit their positions for personal gain.
3. Law Enforcement Challenges:
Investigating check fraud presents unique challenges to law enforcement:
-
Jurisdictional Issues: Fraudulent checks often cross state or international borders, complicating investigations.
-
Technological Sophistication: Fraudsters utilize advanced techniques that require specialized expertise to detect.
-
Resource Constraints: Limited resources can hinder thorough investigations, particularly in cases involving multiple victims or complex schemes.
-
Evolving Tactics: Check fraudsters constantly adapt their methods, requiring law enforcement to stay ahead of the curve.
4. Impact on Innovation:
The rise of check fraud has driven innovation in the financial sector. Banks and other financial institutions are constantly developing new technologies to detect fraudulent checks, such as advanced image processing, machine learning algorithms, and real-time transaction monitoring.
Closing Insights:
The pervasiveness and adaptability of check fraud necessitate a multi-pronged approach to mitigation. Individual vigilance, coupled with technological advancements and robust law enforcement strategies, are essential in combating this persistent threat.
Exploring the Connection Between Identity Theft and Check Fraud
The relationship between identity theft and check fraud is undeniable. Identity theft often provides the foundation for check fraud schemes. Fraudsters use stolen personal information, such as social security numbers, driver's license numbers, and bank account details, to create fraudulent checks or take over existing accounts.
Key Factors to Consider:
-
Roles and Real-World Examples: Stolen identities are used to create entirely new identities for check writing, making tracing back to the original perpetrator incredibly difficult. This can involve creating false addresses, employment history, and even fabricated identification documents.
-
Risks and Mitigations: The risks include significant financial losses for victims, damaged credit scores, and the complex process of restoring one's identity. Mitigating the risks involves robust identity protection measures, such as monitoring credit reports, using strong passwords, and being wary of phishing scams.
-
Impact and Implications: Identity theft connected to check fraud has wide-ranging implications, including damage to individual reputation, increased costs for financial institutions, and erosion of public trust.
Conclusion: Reinforcing the Connection
The symbiotic relationship between identity theft and check fraud highlights the importance of holistic security measures. Protecting one's personal information is not just about preventing identity theft; it is about safeguarding oneself against the secondary financial crimes, such as check fraud, that often follow.
Further Analysis: Examining Identity Theft in Greater Detail
Identity theft forms the cornerstone of many check fraud operations. Understanding the various methods employed by identity thieves – from phishing attacks and data breaches to physical theft of documents – is crucial in understanding the broader landscape of check fraud. Analyzing the common sources of stolen information, such as medical records, social media, and data breaches of major corporations, provides further insights into the vulnerabilities exploited by fraudsters.
FAQ Section: Answering Common Questions About Check Fraud
Q: What should I do if I suspect I am a victim of check fraud?
A: Immediately contact your bank and report the fraudulent activity. File a police report and document all relevant information, including check numbers, amounts, and dates.
Q: How can businesses protect themselves from check fraud?
A: Implement strong internal controls, such as requiring dual authorization for checks exceeding a certain amount, regularly reconcile bank statements, and use check verification services.
Q: What are some technological advancements in fraud detection?
A: Advanced image processing software can detect altered or counterfeit checks. Machine learning algorithms analyze transaction patterns to identify suspicious activity. Real-time transaction monitoring systems flag potential fraud attempts immediately.
Practical Tips: Maximizing the Benefits of Fraud Prevention
-
Monitor bank accounts regularly: Examine statements carefully for discrepancies or unauthorized transactions.
-
Use caution when handling checks: Shred unwanted checks to prevent them from falling into the wrong hands.
-
Implement strong security measures: Use multi-factor authentication and strong passwords for online banking and financial accounts.
Final Conclusion: Wrapping Up with Lasting Insights
Check fraud, driven by sophisticated criminals and enabled by vulnerabilities in the system, presents a significant challenge. By understanding the methods employed by check fraudsters, the importance of identity protection, and the technological innovations combating this crime, individuals and businesses can significantly reduce their risk of falling victim. A proactive and informed approach, combined with a collaborative effort between individuals, financial institutions, and law enforcement, is crucial in winning the ongoing battle against check fraud.
Latest Posts
Latest Posts
-
How To Activate Navy Federal Credit Card
Apr 06, 2025
-
How To Get Approved For Navy Federal Credit Card
Apr 06, 2025
-
Best Time To Apply For Navy Federal Credit Card
Apr 06, 2025
-
How To Prequalify For Navy Federal Credit Card
Apr 06, 2025
-
How To Apply For Navy Federal Credit Union
Apr 06, 2025
Related Post
Thank you for visiting our website which covers about Check Fraudsters . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.